See the full path. Not just the configured access.
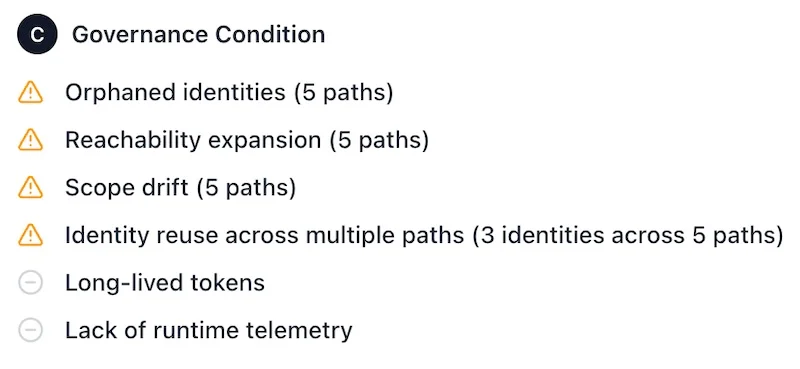
See how automations and agents actually operate across your environment — where they've exceeded intended access, and where ownership no longer holds up.
A fundamentally different approach.
Most tools report on configured access. Securityv0 maps what actually happens when automations execute — and builds the full chain of custody across every system they touch.
100% deterministic
Every finding is structural and replayable. No probabilistic scoring. No ML-generated alerts. No inference. If it's surfaced, it's real.
Full execution path analysis
The complete authority chain — from automation to identity to system to data domain — constructed and mapped automatically across environments.
Metadata-only. Content-free.
Analyzes how systems are connected — not what flows through them. No business content. No ticket data. No payloads. No content inspection, ever.
Not inline. Zero disruption.
Sits outside the execution path entirely. Read-only. No agents deployed. No changes to source systems. Nothing slows down.
Observes what actually runs
Not what's intended. Not what's documented. The executions themselves — the real authority path from automation to data, as it exists in production.
What a finding looks like
Authority path:
ServiceNow automation
→ sn-ticket-router identity
→ Microsoft Graph
→ confidential data domain
Ownership: orphaned
Egress: external
Scope drift: 0 baseline →
3 roles
Complete execution visibility.
Every automation path. Every identity in the chain. Every scope change. Mapped end-to-end — with the evidence to prove it.
Prioritized. Not triaged.
Findings ranked by real operational impact — not alert volume. Your team works the highest-risk items first.
Remediation guidance included.
Every finding ships with the structural change needed to reduce exposure. Not just what's wrong — what to do about it.
Executive-ready evidence.
One-line business risk statements. Audit-grade documentation. Ready for the board, the CISO, or the next compliance cycle.
Deployed in under an hour.
15–20 min
Setup time
Hours
To first findings
Read-only
No agent deployment
EU available
Data stays in-region
One Entra app registration. One ServiceNow API user. Read-only permissions only. No changes to your environment. Designed to fit into existing IAM and security workflows from day one.